Ortelius Blog
Topics include Supply Chain Security, Vulnerability Management, Neat Tricks, and Contributor insights.
AI Automation for Secure Dependency Fixes
Security teams today face a constant barrage of CVE notifications, so many that the signal gets buried in the noise. Over time, alert fatigue sets in, and remediation remains a manual, time-consuming source of engineering toil rather than a fast path to risk reduction.
Updating a dependency is rarely just a version bump. It requires understanding transitive dependency trees, constraint conflicts, ecosystem semantics, and runtime impact. What security teams actually need is not another scanner, but an intelligent remediation agent that behaves like an experienced security engineer.
This post introduces a production-ready architecture for an AI-driven CVE remediation agent designed to analyze dependency graphs, select remediation strategies, and generate validated Pull Requests automatically, without sending proprietary code to external AI services.
Why CVE Remediation Is Harder Than Detection
Most existing tools stop at alerting:
“Package X is vulnerable. Upgrade to version Y.”
But real-world remediation involves:
- tracing transitive dependency paths
- evaluating semantic version constraints
- determining whether parents block upgrades
- deciding between clean upgrades vs overrides
- preserving build stability
- validating fixes through CI workflows
The Ortelius AI Auto Remediation architecture solves those problems using a structured three-tier AI remediation agent model.
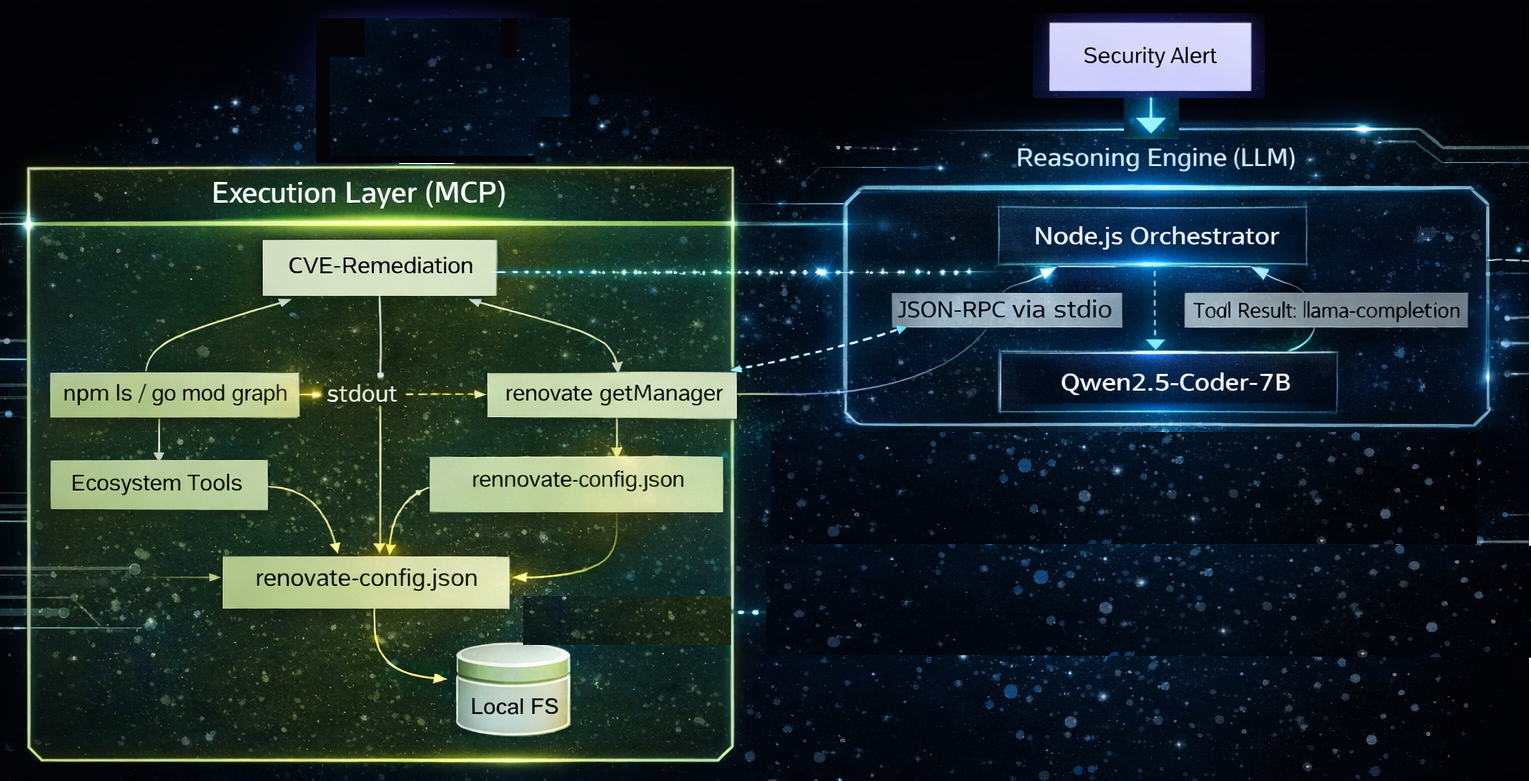
Architecture Overview: A Three-Tier Remediation Agent
The system separates reasoning, orchestration, and execution responsibilities:
| Component | Technology | Responsibility |
|---|---|---|
| The state manager | Node.js Orchestrator | It sequences each inference call, dispatches MCP tools in order, and maintains the llm-renovate.txt context file. |
| The decision maker | Qwen2.5-Coder-7B | It follows the ReAct pattern to determine if a fix requires an update or an override. |
| The capability provider | @modelcontextprotocol/sdk | It exposes 5 specific tools to the LLM and executes Renovate logic programmatically. |
This separation ensures:
- deterministic execution
- schema-safe file changes
- reproducible remediation workflows
- ecosystem portability (Node, Go, etc.)
Instead of allowing an LLM to modify files directly, the model reasons only, while the MCP layer performs execution safely.
From CVE Alert to Verified Pull Request
The remediation lifecycle mirrors the workflow of a senior security engineer.
Step 1: Detection
A vulnerability alert enters the system from a scanner or SBOM pipeline. The agent converts the alert into a structured remediation objective.
Step 2: Dependency Path Investigation
Instead of blindly upgrading packages, the agent:
- maps full dependency paths
- identifies transitive parents
- determines whether exposure is real
- evaluates constraint conflicts
This avoids unnecessary breakage while focusing only on actionable risk.
Step 3: Strategy Selection
The agent chooses among four remediation strategies:
| Strategy | When Used |
|---|---|
| update_transitive | Upgrade nested dependency directly |
| bump_parent | Upgrade parent package |
| override | Apply temporary constraint override |
| no_action_required | Fix already blocked by constraints |
This mirrors real-world engineering decision-making instead of static rule execution.
Deterministic Constraint Analysis (Not Guesswork)
One of the most powerful elements of this architecture is the constraint evaluation engine. Before selecting a remediation strategy, the system runs a structured comparison pass that:
- Pads semantic versions deterministically
- Evaluates lower and upper bounds
- Checks constraint compatibility
- Classifies violations
- Returns a structured JSON decision object
Example:
4.14.6 → v004014006
This guarantees lexicographic ordering across ecosystems and eliminates ambiguity in version reasoning. The orchestrator, not the LLM, decides the strategy based on this output.
This is critical for reliability.
MCP: Separating Thinking from Doing
The architecture uses the Model Context Protocol (MCP) as a capability layer between the LLM and the filesystem.
This creates a strict boundary:
- The LLM can reason
- The MCP tool executes
Example workflow:
LLM selects strategy
↓
Calls generate_renovate_config
↓
MCP validates parameters
↓
Writes configuration file
↓
Runs Renovate modules locally
The model never writes package manifests directly. This eliminates hallucinated config errors and guarantees schema validity.
Renovate as the Execution Engine
Instead of generating patch suggestions manually, the system embeds Renovate modules directly into the remediation loop. The agent produces a real Pull Request containing:
- manifest updates
- lockfile recalculation
- dependency corrections
- version overrides if required
This keeps remediation aligned with existing CI/CD workflows:
-
Engineers review the PR before merge.
-
Human-in-the-loop safety is preserved.
Tooling Provided by the MCP Server
The remediation agent exposes five structured execution tools:
| Tool | Function |
|---|---|
| get_dependency_paths | Finds vulnerable package entry paths |
| check_parent_fix | Tests whether upgrading parent resolves issue |
| apply_override | Applies constraint override if needed |
| generate_renovate_config | Builds remediation configuration |
| run_local_renovate | Executes patch generation |
Each tool represents a deterministic remediation step. Together they form a repeatable vulnerability-to-PR pipeline.
Why This Architecture Works Better Than Traditional Fix Bots
Typical dependency bots:
- bump versions blindly
- ignore runtime exposure
- cannot resolve constraint conflicts
- generate noisy PRs
- create upgrade fatigue
The Ortelius AI agent instead:
✔ traces dependency graphs
✔ evaluates semantic compatibility
✔ selects remediation strategy intelligently
✔ executes fixes safely
✔ produces reviewable PRs
It behaves like a security engineer inside your pipeline.
The Strategic Advantage: AI + Structured Execution
This architecture demonstrates something important about the future of software supply chain security:
-
The next generation of remediation tooling will not be scanners.
-
They will be reasoning agents with controlled execution boundaries.
By combining:
- LLM reasoning
- deterministic constraint analysis
- MCP capability isolation
- Renovate automation
Teams can move from alert-driven security to resolution-driven security.
Where This Fits in the Future of Automated Remediation Platforms
This design pattern aligns directly with emerging approaches in post-deployment vulnerability defense, especially platforms that focus on identifying which vulnerable components are actually running in production environments and prioritizing remediation accordingly.
When runtime visibility is combined with intelligent remediation agents like this one, organizations gain:
- attack surface awareness
- constraint-aware patch automation
- SBOM-driven remediation prioritization
- reduced MTTR for critical CVEs
That is the foundation of continuous vulnerability defense.
Not just detection, but closure.
Supporting Air-Gapped and Highly Regulated Environments - On-Prem with Loacl AI Agent
While most users will interact with Ortelius via the SaaS environment, some will require an on-premise installation of Ortelius, with a local AI-agent. Security-sensitive environments, including defense, regulated enterprise, and HPC infrastructure, cannot send source code to cloud AI APIs. An on-premise installation with local AI agents will satisfy the needs of these highly secured environments.
The local AI Agent system runs entirely locally using:
- Qwen2.5-Coder-7B
- llama.cpp
- GGUF model format
- MCP tool interfaces
Result:
No proprietary code leaves the machine.
This makes the architecture viable for:
- air-gapped systems
- classified environments
- enterprise software factories
- space and defense pipelines
- regulated CI/CD infrastructure
Conclusion and Get Involved: Help Build the Future of AI-Driven Remediation
Automated CVE remediation is entering a new phase, moving beyond detection toward intelligent, constraint-aware resolution that operates safely inside real development workflows. This architecture represents an important step toward that future, but it is only the beginning.
We invite contributors who are interested in dependency intelligence, SBOM-driven security, Model Context Protocol (MCP) tooling, local LLM orchestration, and automated vulnerability remediation to join the Ortelius community and help shape this work. There are opportunities to contribute across the stack, from dependency-path analysis and remediation strategy logic to MCP tool integrations and workflow automation inside modern software factories.
Watch for upcoming Ortelius releases that will begin delivering these AI-assisted remediation capabilities as part of its broader mission to provide continuous, post-deployment vulnerability visibility and response. Together, we can move the industry from alert fatigue to automated resolution, and make continuous vulnerability defense a practical reality.
